https://www.youtube.com/live/Xs7rp-JLzOI?si=GC_If7JQj1NgSYvw


SEARCH / DOTS911 #LIFE #SAVING APP PROJECT
Shared / July 29, 2019 & Re-shared / Sept. 19, 2023
#WHAT IS THE DOTS911 #PROJECT ALL #ABOUT?
(Take a Look at the #Dots911 Video)
Dosehit Network Aurora Corporation
#Dots911 is three interconnected products: a mobile signal strength and navigation app, a cloud-hosted map database, and a hardware signal enhancer. Unlike me-too alternative mapping products, #Dots911 offers truly unique functionality with direct world-changing utility.
The #Maps1 App is fun, but it could also easily save your life.
================================================
================================================
================================================
#1. The mobile app collects signal strength and other parameter data as a function of the user's latitude and longitude. This creates a map for the user, showing the shortest navigable path back to a location with a good mobile phone signal. The fact that these are navigable paths, not just a series of signal strength data points, is critically important because it means a user can follow a path dataset of colored dots to a #useable signal along safe roads, trails, or other routes with no obstructions. No competitive product offers these features, which we own through granted patents, and which enable a user in an emergency to pull out a phone and walk directly to the nearest location with a #useable signal along a guaranteed-safe route.
((( #FIND + App Installation Instructional Detail Video )))
#2. The cloud-hosted map database is a collection of data collected by the mobile app and a map layer interface well-suited for value-adding inclusion as a layer in existing commercial mapping software, enabling collection and dissemination of these data. No online signal mapping competitor offers point-based or navigable path-based data and our patented path selection method is superior in efficacy and clarity to any existing path selection interface in any software for any type of sequential location-based data. The website can show stories of how people navigated using the dots to hopefully convert a bad scenario to a mere inconvenience, and not be part of a tragic news broadcast.
#3. The hardware signal enhancer is a unique low cost, lightweight, portable, directional device that is simpler and more portable than any other effective signal enhancer on the market, which #synergizes with the signal and navigation app by enabling mobile service in locations with extremely poor or no signal when using only a phone’s internal hardware. Previous signal enhancers have either been active, requiring powered hardware or fraudulent. Ours is neither, and unlike most historical signal enhancers, it works with any phone without requiring any physical port.
===================================================
===================================================
===================================================
We’re interested in exclusively licensing our technology to a platform owner who can implement it as part of a mapping platform with a large existing user base. If you license our products and IP portfolio, you’ll have a unique competitive advantage over your competitors that will likely save hundreds to thousands of lives per year in the United States alone, resulting in unbeatable publicity advantages over rival mapping platforms and mobile device manufacturers. Please contact us for discussion.
#contact: JRW@dots911.com
==========================
#Source: Dave Wilbur
Dosehit Network, LLC
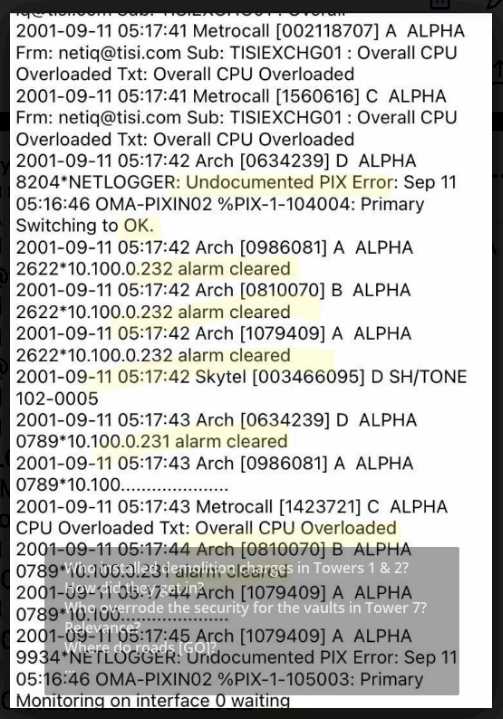
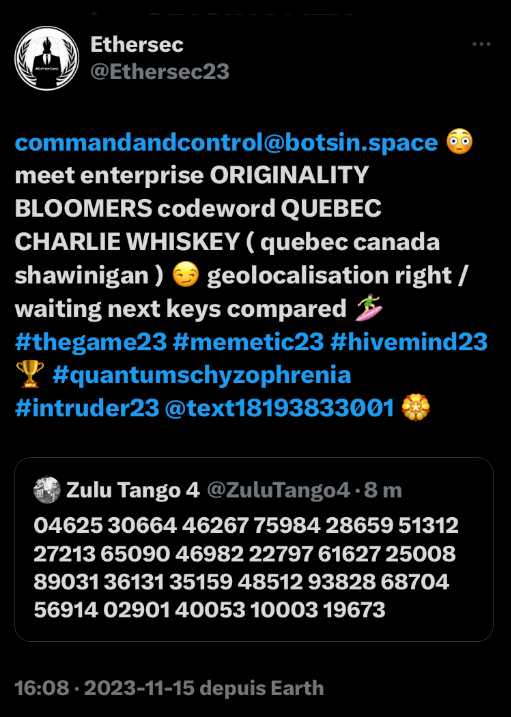
Non-memetic cyberwarfare tactics and techniques typically refer to strategies and methods that do not rely on the manipulation of memes or cultural content to achieve their objectives. Instead, they focus on traditional cyber warfare approaches. Here are some examples:
1. DDoS Attacks: Distributed Denial of Service (DDoS) attacks involve overwhelming a target’s online services with a flood of traffic, causing them to become unavailable to users.
2. Malware Deployment: Cyber attackers use various forms of malware, such as viruses, worms, Trojans, and ransomware, to infiltrate systems, steal data, or disrupt operations.
3. Phishing: Phishing attacks involve tricking individuals into revealing sensitive information like login credentials or credit card details by posing as a legitimate entity through email or fake websites.
4. Zero-Day Exploits: Cyber attackers may discover and exploit vulnerabilities in software or hardware that are unknown to the vendor, gaining unauthorized access to systems.
5. Man-in-the-Middle (MitM) Attacks: In MitM attacks, attackers intercept communication between two parties, potentially eavesdropping or altering the messages exchanged.
6. Advanced Persistent Threats (APTs): APTs are long-term, targeted cyberattacks in which adversaries maintain unauthorized access to a network to gather information or conduct espionage.
7. Data Breaches: Attackers breach databases and steal sensitive information, which can be used for financial gain or other malicious purposes.
8. Brute Force Attacks: In these attacks, attackers attempt to gain access to a system by systematically trying all possible password combinations until they find the correct one.
9. Supply Chain Attacks: Cyber attackers compromise the supply chain of a target organization, injecting malware or vulnerabilities into software or hardware components before they reach the target.
10. Cyber Espionage: Nation-states and threat actors may engage in cyber espionage to gather intelligence, trade secrets, or sensitive information from government or corporate entities.
These tactics and techniques are part of the broader field of cyber warfare and cybersecurity, and they are used for a variety of purposes, including espionage, financial gain, disruption, and more. Countermeasures, such as strong cybersecurity practices, threat intelligence, and incident response plans, are crucial for defending against these threats.
Sure, I can explain neural networks in a simple way!
Think of a neural network as a computer system that tries to mimic how our brain works when we learn things. It’s made up of tiny computing units called neurons, just like the ones in our brains.
Here’s how it works:
1. Input: You give the neural network some information, like pictures of cats and dogs. Each piece of information is broken down into smaller parts, like the colors and shapes in the pictures.
2. Processing: The network takes these small pieces of information and combines them in different ways, just like how our brain processes information when we look at things. It does this by using math and learning from lots of examples.
3. Output: After processing, the network makes a guess about what it’s looking at. In our example, it might guess whether the picture is a cat or a dog.
4. Learning: If the guess is wrong, the network learns from its mistake. It adjusts how it combines the information to make a better guess next time. This learning process happens over and over with many examples until the network gets really good at guessing.
So, a neural network is like a computer brain that learns from examples to make educated guesses. It’s used in things like recognizing faces in photos, understanding spoken language, and even playing games like chess or Go. It’s a powerful tool for solving complex problems!